The key lesson learned from rising security threats is obvious. Adversaries have advanced their capabilities and can work together to improvize attacks for breaching security systems and controls. Contrary to expectations, even large enterprises are either incapable or unaware of their shortcomings in security posture. Though companies have the motivation and budget to focus on enhancing security, most invest in siloed tools with disjointed workflows that invariably increase the cost and complexity of operations. This results in poor visibility resulting in more blind spots, missed threats, and a continuous struggle to keep up with the rising sophistication of attack vectors.
To avoid any state of dysfunction and ensure a higher state of readiness, the capabilities of SOC must be evolved, keeping in mind the rapid rise in the scope and scale of security operations due to digital transformation. Security teams need advanced SIEM solutions that offer centralized visibility into security data and insights on top priority threats while integrating detection, investigation, and response to avoid strategic security mistakes. These SIEMs also leverage automated analytics and threat intelligence to fasten investigation time. In addition, they scale rapidly with out-of-the-box use cases and integrations to mitigate regulatory risks.
IBM QRADAR
One such tool is IBM QRADAR – a comprehensive cloud-native extended detection and response (XDR) solution that integrates security tools, such as endpoint detection and response, network detection and response, SOAR, threat intelligence, processes, people into one workflow. QRADAR XDR is the best open threat detection, investigation, and response tool. The largest open XDR ecosystem, QRADAR, supports a wide range of technologies, applications, and cloud services. It offers fewer accurate alerts with streamlined workflows and reduces manual efforts through AI-driven automation. With pre-built detection and response tools, it can even be operated by security teams who don’t have deep security expertise.
The tool can empower security analysts to meet their operational objectives by giving them 360o visibility by collecting, parsing, and normalization of disparate log and flow data, events, network flows, cloud applications, user activities, vulnerability information, and threat intelligence, helping them detect threats and maintain compliance accurately. The data is centralized for automated analysis of threats, anomalies, and risks.
By including more than 450 pre-built device support modules, it can be seamlessly integrated into other security tools. QRADAR can automatically detect the log source type and apply the suitable device support module to analyze and normalize log data. Automatic identification and classification of assets can be made using this tool by inspection of network data. Asset classification is based on the applications, protocols, services, and ports used.
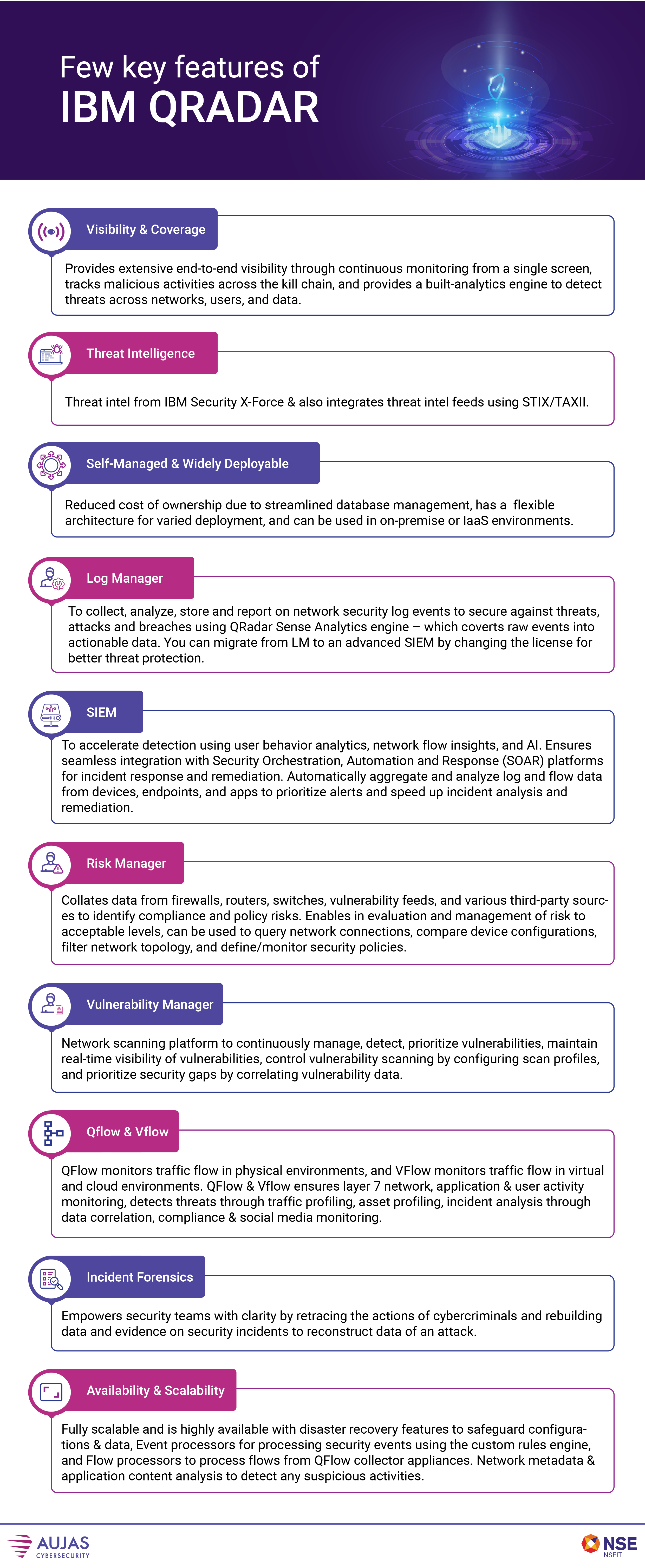
IBM QRADAR XDR can correlate alerts and prioritize them for security analysts, helping them to cut through the clutter of alerts from multiple tools. By leveraging AI, QRADAR can automatically investigate cases to enhance analysts’ efficiency enabling them to focus more on threat hunting. The tool also uses MITRE ATT&CK mapping and threat intel for improved alert prioritization, root cause analysis, and response. QRADR, being an open security platform, gives you the choice of selecting the security tool you want and can also connect a range of tools to modernize your SOC.
To know more about IBM QRADAR, and how it can help you modernize your security operations, do get in touch with our experts at contact@aujas.com.





